
The COVID-19 pandemic has been a catalyst for digital adoption across the UK for businesses and consumers alike. However, the increase in digital usage has brought a combination of opportunities and challenges, especially for organizations in banking and fintech. Particularly challenging has been the need to quickly onboard huge influxes of new users to existing online services. Customers used to doing their banking activities in person are now suddenly compelled to use the bank’s digital equivalent. For many, a big hurdle is figuring out how to provide remote identity proofing of personal information in order to establish trust for using these digital services.
Banks have inconsistent processes for remote identity proofing
 Remote identity proofing is the process of an online customer confirming their ownership of a claimed identity. For banks, the ability to check someone’s identity is an essential step for enabling digital transactions. It’s a delicate balance between building out robust fraud prevention systems that comply with AML and KYC regulations and providing a good customer experience. This fundamental security need has to be tempered with an amount of friction that customers are willing to accept. Ultimately, the goal for banks is to validate identities in a fast, frictionless, and effective way.
Remote identity proofing is the process of an online customer confirming their ownership of a claimed identity. For banks, the ability to check someone’s identity is an essential step for enabling digital transactions. It’s a delicate balance between building out robust fraud prevention systems that comply with AML and KYC regulations and providing a good customer experience. This fundamental security need has to be tempered with an amount of friction that customers are willing to accept. Ultimately, the goal for banks is to validate identities in a fast, frictionless, and effective way.
An identity is a combination of multiple attributes or characteristics that belong to a person. So, a single attribute is usually not strong enough to prove someone’s unique identity. Rather, the strongest line of defense for organizations is to use a combination of attributes. This increases the efficiency and effectiveness of their validation processes. However, with so many attributes that can be used to verify a person’s identity, verification processes within the industry are fragmented and inconsistent across the region.
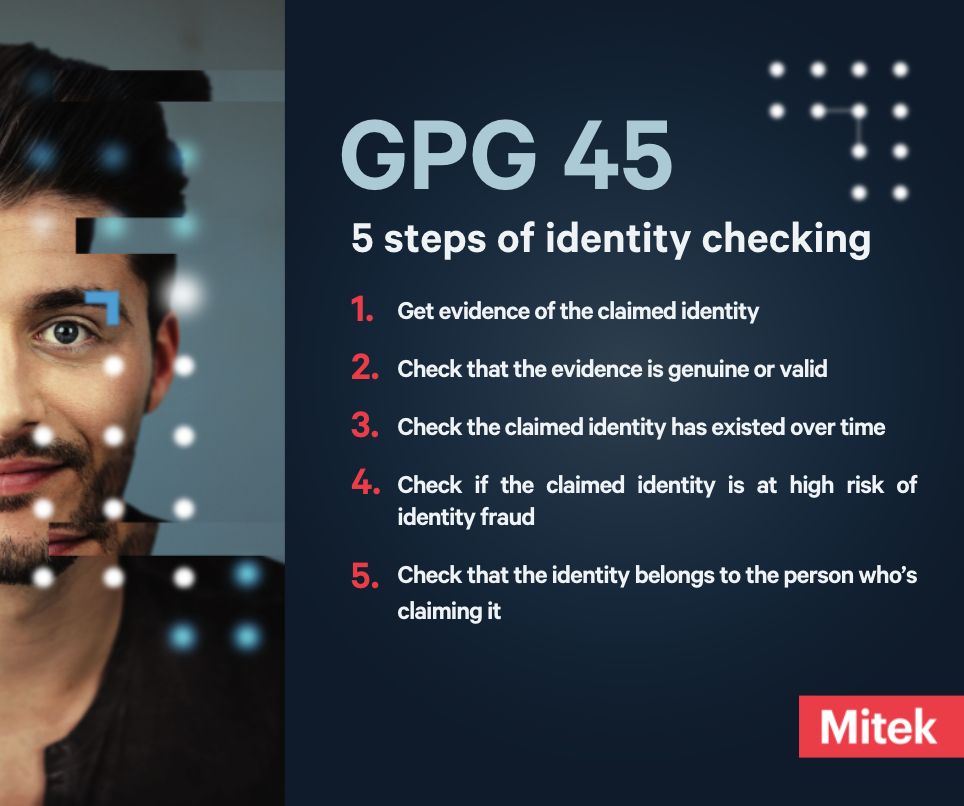
To help drive consistent and widespread standards, the UK government has published guidance on how to prove and verify the identity of a customer or an employee. These guidelines are referred to as Good Practice Guide 45 (GPG 45).
Click here to learn more on establishing trust throughout the digital identity lifecycle
How to use GPG 45
GPG 45 does not dictate a specific process for checking an identity. Rather, it is designed to help companies understand various identity verification methodologies and choose the ones that best suit the needs of their organization. Ultimately each organization must take into consideration both internal and external requirements (such as regulatory obligations) and then decide what tools or processes they want to use based on their needs.
For example, an organization might decide to accept a passport as evidence of someone’s id document if they know:
- The users of their service are likely to have a passport
- The staff in their organization have the equipment they need to check the document’s validity
So, how does GPG 45 work? It starts by breaking down the identity checking process into five steps:
- Get evidence of the claimed identity
- Check that the evidence is genuine or valid
- Check the claimed identity has existed over time
- Check if the claimed identity is at high risk of identity fraud
- Check that the identity belongs to the person who’s claiming it
A score of one to four is then assigned to each of the identity checking steps based on the pieces of evidence collected. The scores for each part of the identity checking process can then be combined in several ways to achieve a final confidence score. These combinations are known as identity profiles.
An identity profile relates to a level of confidence (i.e. Low, medium, high, and very high) that an organization can have in trusting the verified identity. By reaching a higher level of confidence, an organization or service can measure how well it is protected against identity risks. Ultimately, its identity checking process can be reused or reaffirmed by other organizations and services.
Mitek provides support to organizations across the different parts of the GPG 45 self-attestation process to help them accomplish different levels of identity profile confidence. We’ve outlined how our technology helps within each part.
Part 1:
Mitek supports the highest level of confidence for gathering evidence of the claimed identity through our NFC technology. NFC provides near-perfect data extraction and deterministic authentication against government-issued certificates for eDocuments (ICAO Doc 9303 Passports, Identification Cards, Drivers Licenses). The data present inside an NFC chip includes the document holder's data and their digital photo.
Part 2:
Mitek helps organizations reach a maximum score in confirming the evidence is valid. We check that the evidence has not been canceled, lost, or stolen, as well as confirm that physical security features are genuine and the evidence has not expired. These checks often require a 3rd party authoritative source, so businesses might need to incorporate external data sources to meet this requirement. To reach a score of four (i.e. The highest level of confidence), additional checks must be implemented, such as confirming that the UV, IR, or cryptographic security features on the evidence are genuine.
Part 3:
In order to evaluate Part 3’s “Check the claimed identity has existed over time”, GPG 45 recommends database checks to ensure there are records that show the claimed identity has regularly interacted with other organizations or people. These checks can include credit card transactions, gas or electricity account payments, or employment or health records. Through services like our Bank Connect offering, Mitek provides assistance with this check.
Part 4:
The highest possible score for Part 4 of the identity verification process is a three. This part is focused on ensuring that the claimed identity is not at a higher than usual risk of identity fraud or suspected to be a synthetic identity. An organization can do this by checking the details of the claimed identity with authoritative counter-fraud data sources, such as a national fraud database. Mitek connects you to multiple, independent authoritative sources that enables you to reach the maximum confidence score for this section.
Part 5:
Part 5 focuses on verifying that the identity belongs to the person who’s claiming it. To get a score of four, you need to make sure the biometric information of the person in question, such as a fingerprint, matches biometric information from the strongest piece of genuine evidence you or an authoritative source has.
An example is comparing a face in real time to a government issued ID. Spoof detection is critical for verifying authenticity in this section. Organizations must include protection against multiple types of sophisticated presentation attacks, such as the use of a 3D animated avatar on a hijacked computer or device. Mitek’s liveness detection process is a powerful and reliable way to verify that the person on the other end of the device is the authentic owner of the identity in question.
Mitek provides the strongest line of defense against ID fraud in the UK
Mitek has a diverse range of powerful and effective solutions to meet the UK government’s standards for identity verification against many different levels of assurance. Clients deploy KYC journeys that are customized to verify identities based on product, market, or fraud risk. Identities are verified in a consistent way that not only accelerates onboarding but simultaneously reduces fraud. To learn more about how Mitek can help you implement compliant and the strongest GPG 45 practices.