
Multi-factor authentication (MFA) is a method of electronic authentication in which two or more factors (eg. a password and voice recognition) are required for a user to gain access to a website or application. These factors could be in the form of knowledge (something only the user can know), inherent characteristics (something only the user can be), or possession (something only the user can have). MFA is designed to be more secure than a simple login using an ID and a password, protecting the user from identity theft and fraud.
How authentication works
The concept of authentication is quite simple. The user has to prove their identity to a server, website, or platform to gain access to it. Traditionally, the authentication process involved a single factor step, like logging in with a username and password. But it can be easy to compromise password credentials, especially if they are simple to guess, like “1234” or “password”. And if an individual uses the same password for multiple accounts, access to one password for a seemingly insignificant account a user opened years ago can enable fraudsters to hack important accounts like company databases, bank accounts, and more. The problem with passwords is that they can be troublesome to remember for users, and costly for companies to institute strict password policies that will truly protect company data. According to Javelin’s report, Consumer Preference Drives Shift in Authentication, 22% of identity fraud victims had their passwords and email credentials stolen in 2020. While 75% of consumers say passwords are one of the easiest authentication methods, they also understand that passwords are easily compromised.
In this case, multi-factor authentication can be used as an extra step and additional hurdle for fraudsters to cross when attempting to access an account. Even minor factors like a secret question could discourage hackers from accessing data. Fortunately, technology has evolved quickly and much more sophisticated and stronger authentication methods are available to keep data secure.
Download Javelin's new white paper - - Consumer preference drives shift in authentication
Types of authentication
With fraud on the rise, it's more important than ever to implement extra layers of security for business, employees, and customers using two or three of these MFA factors:
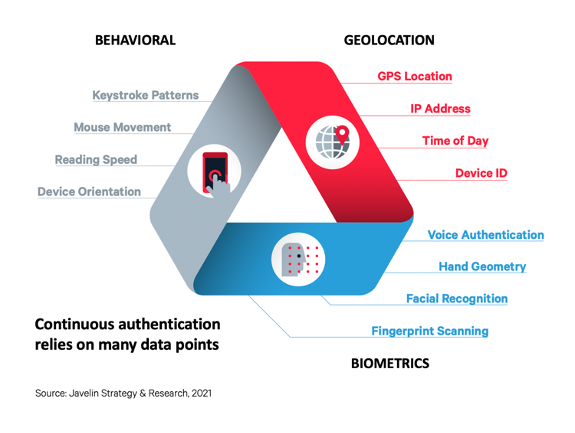
- Something you are:
This is information that is part of the user. It’s a characteristic, or biometric, that only the user possesses. This includes, but is not limited to, facial recognition, voice recognition, biometric scans such as the fingerprint, handprint and retina. Confidence in biometric authentication is steadily increasing according to the Javelin study. Consumers’ perceived effectiveness of facial recognition (63%) and retinal scanning (62%) remained steady from 2019 to 2020, but voice recognition for the first time finally reached a 50% perceived effectiveness rate. - Something you have:
This has to do with information the user can physically carry with them. Examples include identification like a work ID card, a passport, a personal identity verification (PIV) card, an authentication app, or a token (also called a one-time password), usually sent via SMS/push notification. These verification methods are usually used in two-factor authentication, along with something you know. - Something you know:
This is information that the user stores in their own memory (or has it written down or recorded somewhere) and can retrieve when needed. Examples include a password, a Personal Identification Number (PIN), a security key, or the answer to a security question (like your mother’s middle name, the street you grew up on, your first pet’s name, the name of your best friend, or the city you were born in). - Somewhere you are:
This factor is not as well known as the ones mentioned above. This is related to your physical location. Some of the methods for detecting a user’s location include via their Internet Protocol (IP) address, their media access control (MAC) address, or the geolocation on their mobile phone or device.- IP Address is a numerical label assigned to every device connected to a computer network that uses the internet for communication. It is the most common method to detect a user’s location. For example, the IP address would tell if the user is logging in from the US vs Germany.
- MAC address is a unique identifier assigned to a network. A company may set up its network so that only specific computers (with fixed MAC addresses) can be used to log in. If someone tries to access the network from another computer, they will be denied access.
- Mobile geolocation uses the GPS location on the user’s phone to detect their location. If a user’s last known location was in the United States and a couple of hours later, the card is used in India, it could mean that the user is not in the same location as the card.
- Something you do (habits and behaviors):
This is the least utilized factor of all the types of authentication mentioned so far, mainly because it’s not as well known. This type of authentication proves the user’s identity by observing their actions. These actions include:- How fast you type
- How you move your mouse
- Keystroke dynamics
- Signature dynamics
- Gestures and touches
- Speech patterns
Multi-factor authentication vs multi-step authentication
Sometimes, instead of multi-factor authentication, companies utilize multi-step authentication. The difference between the two is that multi-step authentication verifies each factor separately, one after the other, while multi-factor authentication validates them all at once.
For example, in a system that requires a username and password followed by a token, if the authentication is multi-step, the username and password is validated first, followed by the token. If it is multi-factor authentication, the system only validates the username and password once the token is provided. The advantage of the latter approach over the former is that in this case, if login fails, one does not know if the username, password, or the token was wrong.
Multiple authentication factors are thus a stronger approach if you want to protect your data and that of your company without the hassle of getting your employees to change their passwords too frequently or risking forgetting their passwords and usernames. Taking the layered approach a step further, Javelin also recommends continually verifying a consumer’s identity throughout the customer lifecycle via a variety of checks, which will significantly reduce the chance of identity fraud or unauthorized account access.